Feedly’s Vulnerability Intel Agent now includes powerful CVSS Vector filters that give you precise control over CVE prioritization based on attack methods and impact. Instead of relying solely on CVSS scores, you can now target vulnerabilities based on how they’re exploited and what systems they affect.
Filters use Boolean logic (AND/OR/NOT) across different attributes, including the new CVSS Vector components that break down vulnerability characteristics by attack surface and necessary conditions.
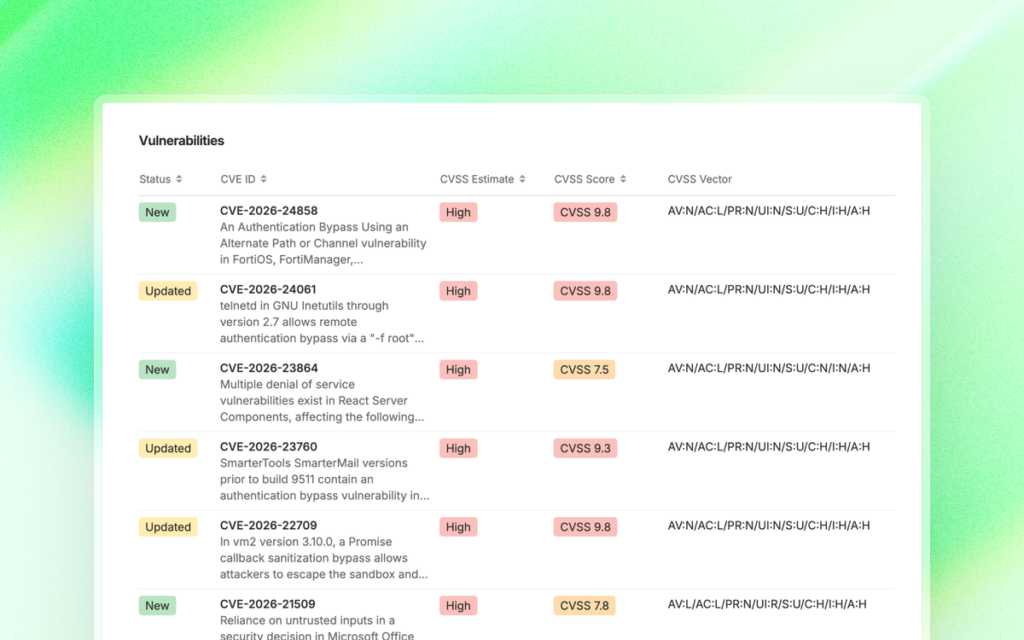
Here are seven examples showing how CVSS Vector filters help you quickly find the vulnerabilities that pose threats to your environment.
Understanding CVSS Vector components
The new CVSS Vector filters turn abstract CVSS scores into practical intelligence:
Attack Vector tells you the vulnerability’s accessibility. Network means reachable from anywhere online. Adjacent Network means the same network segment. Local requires system access. Physical requires in-person access.
Privileges Required indicates if an attacker needs existing system rights. “None” means unauthenticated attacks. “Low” means a basic user could exploit it. “High” would require admin or system access to exploit the CVE.
User Interaction shows if social engineering or user action is needed. “None” implies it’s a fully automated exploitation. “Required” means you have a window to detect and block.
Impact Scope (Confidentiality, Integrity, Availability) clarifies the threat. High “availability” impact means service disruption. High “confidentiality” indicates data exposure. High “integrity” would include a system compromise or data modification.
Scope Change shows if the vulnerability crosses trust boundaries. “Changed scope” implies lateral movement, privilege escalation, or cross-component attacks are now possible.
Example 1: Which unpatched vulnerabilities require zero attacker preconditions and are likely to be exploited?
Identify the most aggressive class of threats: those that are actively exploited and can be exploited upon delivery. This filter combines real-world exploitation status with “wormable” characteristics (no privileges required, no user interaction). Since these vulnerabilities don’t have any patch available, consider implementing compensating controls or detection mechanisms around affected systems.
Filter configuration
(Privileges Required: None)
AND
(User Interaction: None)
AND
(Exploited) OR (Proof of Concept) OR (Weaponized) OR (CISA KEV)
AND
(Attack Vector: Network)
NOT
(Patched)
Result
Example 2: Which remote vulnerabilities threaten your service availability?
When your organization relies heavily on service availability, you need to identify vulnerabilities that could result in remotely exploitable denial-of-service attacks. This filter combines high availability impact with a network attack vector to reveal vulnerabilities that could allow remote attackers to knock your services offline. These high-impact risks and threats are a key concern for customer-facing apps and core infrastructure, where downtime directly impacts your business.
Filter configuration
(Availability Impact: High)
AND
(Attack Vector: Network)
Result
Example 3: Which exploited CVEs are most likely to be remotely exploited?
Identify vulnerabilities that are actively being exploited AND can be exploited remotely. This filter focuses on vulnerabilities that have a proof of concept or have been proven to be exploitable and reachable across the network. Combining real-world exploitation evidence with a network attack vector confirms that adversaries are already using these techniques or will likely at least try; verify if your externally facing infrastructure has been targeted.
Filter configuration
(Exploited) OR (Proof of Concept) OR (Weaponized) OR (CISA KEV)
AND
(Attack Vector: Network)
Result
Example 4: Which remote vulnerabilities pose a major risk of data theft?
Protect your organization from external data breaches by targeting vulnerabilities that could allow a remote attacker to compromise the confidentiality of your data. By combining high confidentiality impact with a network attack vector, you identify CVEs that allow the exfiltration of or access to sensitive information, such as customer records or proprietary code, without requiring physical or local access to the system.
Filter configuration
(Confidentiality Impact: High)
AND
(Attack Vector: Network)
Result
Example 5: Which vulnerabilities expose data without user interaction?
Find “silent” risks where data is exposed without a user clicking a link or opening a file. High confidentiality impact combined with no user interaction means attackers can automate data theft. These vulnerabilities are particularly dangerous for backend systems and databases that process sensitive information, as exploitation can occur in the background without alerting staff.
Filter configuration
(Confidentiality Impact: High)
AND
(User Interaction: None)
Result
Example 6: Which vulnerabilities are low hanging fruits for threat actors?
Attacks with low Attack Complexity require minimal effort to exploit but can have a great impact on your network and are like low-hanging fruit for threat actors. Add in the network vector, and threat actors can attack these vulnerabilities remotely. These attacks are usually some type of injection, or Cross-Site Script.
Filter configuration
(Attack Complexity: Low)
AND
(Attack Vector: Network)
Result
Example 7: Which vulnerabilities allow lateral movement (scope change)?
Track scope-changed vulnerabilities because they can expand the attack surface beyond the initially vulnerable component. When the scope changes from “unchanged” to “changed,” the vulnerability can impact systems outside the directly vulnerable component. When paired with network or adjacent network attack vectors, these CVEs represent dangerous situations in which compromising one system can lead to unauthorized access to others. This is particularly critical in cloud deployments, containerized environments, and segmented networks, where lateral movement can cause a cascade failure.
Filter configuration
(Scope: Changed)
AND
(Attack Vector: Network) OR (Attack Vector: Adjacent Network)
Result
Start prioritizing with CVSS Vector filters
CVSS Vector data can do more than help you prioritize patches. Vulnerability management is actually a good place to start threat hunting because you’re working with real weaknesses in your stack, not theoretical threats. Identify the vulnerabilities that are in your environment using scan results and then apply these filters to begin discovering attack paths that may exist.
Try the Vulnerability Agent available in Feedly Threat Intelligence
Prioritize CVEs by how they’re exploited, not just their severity score.
Start Free Trial